MOBZec Security Explorer
When you have a large network disk with lots of different access rules it can be hard to keep track of who can do what where. Often, disks start out simple (nobody can write in Apps, nobody can execute in Data) but for all kinds of reasons directories can develop different permissions. Windows is not particularly good a showing those permissions, other than directory by directory - or file by file.
What we're interested in is "explicit" access rules. Normally, security on a directory or file is inherited from the parent directory. We can't really says if a directory's permissions are correct, but we could determine whether thery're explcit, i.e. non-inherited.
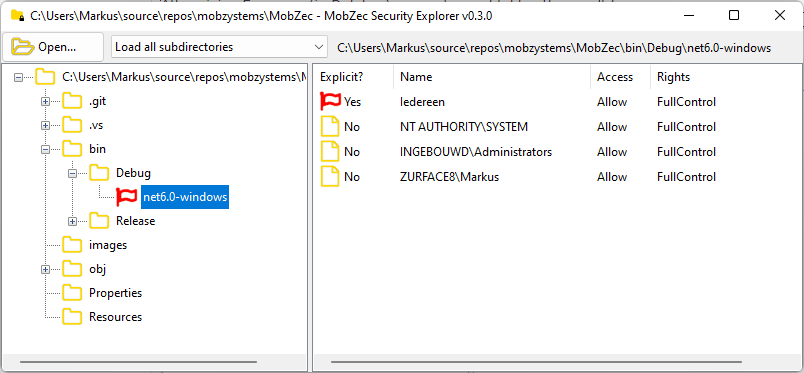
Enter MOBZec. Basically your run-of-the-mill Explorer-like interface (directory structure on the left, access rules on the right) that highlights folders with explicit permissions. In the screenshot below you can see the Windows-directory on my laptop:
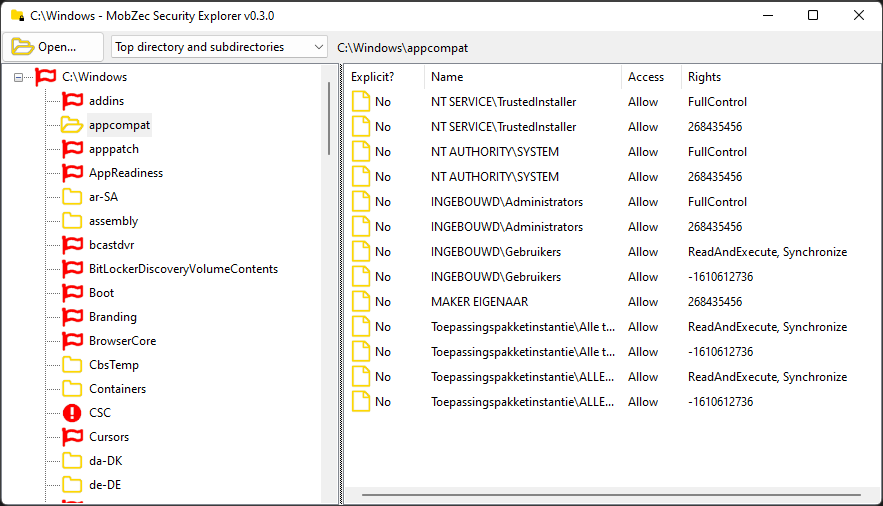
As you can see, the directories the left are either marked with a yellow folder icon, a red flag or a red exclamation mark. The folder icon means the directory has no explicit permissions - i.e. all permissions are simply inherited from the parent directory. The appcompat-directory is selected on the left, and on the right only non-explicit access rules are shown. A folder below it is called debug and it has the following permissions:
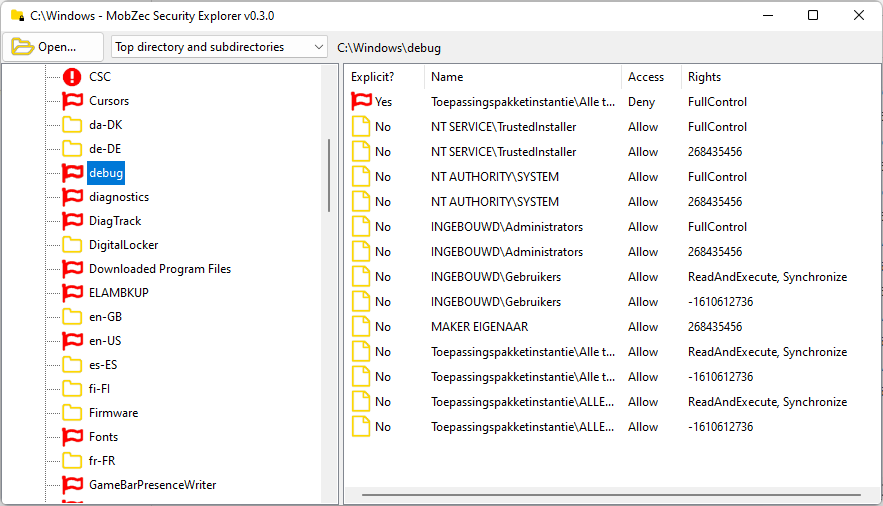
The directory is marked with a red flag and sure enough, the top access rule on the right is an explicit one.
When a folder is marked with a red exclamation mark (like CSC in the screenshot above) you don't have permission to view its permissions. A meta error ;-)
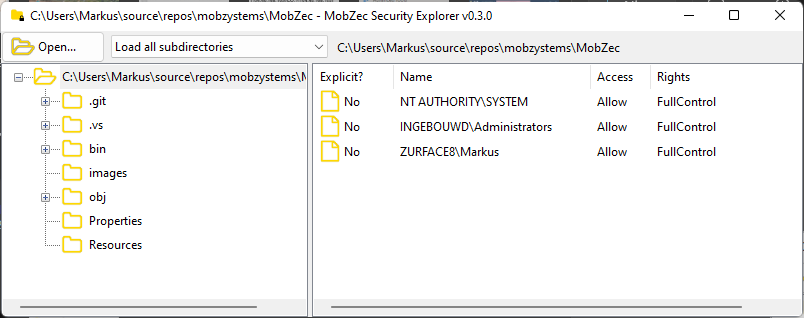
In a nutshell, that's it. There are some quality-of-life features: subdirectories with explicit permissions are always expanded in the directory list on the left, so if all permissions are inherited, the list is "clean":
After giving Everyone (in Dutch...) access to a subfolder, the result becomes:
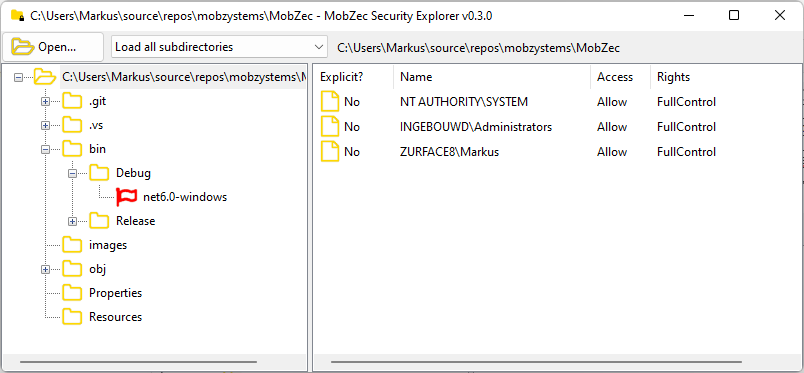
The "explicit" directory is shown and sure enough, when we select it we see the explicit rule on the right:
Next to the Open button is a dropdown list with options:
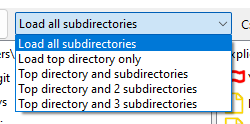
- Load all subdirectories is the default option. It loads security on all directories and subdirectories. This can take a log time on a large network drive, and in most cases deeply nested directories don't have explicit permissions. To get a feel for a directory tree fast, you can also select:
- Load top directory only. This is the opposite: it will show the security on the top directory only - no subdirectories at all.
- Top drectory and subdirectories shows only the immediate cild-directories of the top directory, i.e. two levels
- Top drectory and 2 subdirectories shows three levels
- Top drectory and 3 subdirectories shows four levels.
You can specify the top directory and the number of levels on the command line:
path-to\MOBZec [<path> [<depth>]]
path can be an absolute or relative path (i.e. "." or ".."). depth is 0 by default, meaning all subdirectories; an positive number shows that many levels (i.e. 1 is the top directory only).
Customizable context menus
I was about to add right-click context menus for both the directory tree view and the rule list view when I realized I could use PowerShell for this. I wanted to show all members of a group when right-clicking on a rule. In PowerShell this is easy: in C#, it's hard. And rather specific - you might want other context menu possibilities. So this somewhat derailed and MOBZec now has a customizable context menu system. Anyway, here's how that works:
In MOBZec.dll.config appSettings are used to specify what context menus to show. Here's a sample:
<?xml version="1.0" encoding="utf-8" ?>
<configuration>
<appSettings>
<!-- The command can start with powershell: pwsh: cmd: shell: or nothing -->
<!-- Rule commands start with 'rule:'. #ID# will be replaced with the SID, #NAME# with the name of the account -->
<add key="rule:Show direct group members" value="pwsh:Get-AdGroupMember -Identity "#ID#" | Select-Object SamAccountName, Name | Sort-Object SamAccountName, Name | Out-GridView -Title 'Direct members of group #NAME#'"/>
<add key="rule:Show all group members" value="pwsh:Get-AdGroupMember -Identity "#ID#" -Recursive | Select-Object SamAccountName, Name | Sort-Object SamAccountName, Name | Out-GridView -Title 'All members of group #NAME#'"/>
<!-- Directory commands start with 'dir:'. #PATH# will be replaced with the full path -->
<add key="dir:Open in Explorer" value="explorer.exe "#PATH#""/>
<add key="dir:Reveal in Explorer" value="explorer.exe /select,"#PATH#""/>
<add key="dir:Show contents in PowerShell" value="powershell:Get-ChildItem "#PATH#" | Out-GridView"/>
<add key="dir:Show contents in pwsh" value="pwsh:Get-ChildItem "#PATH#" | Out-GridView"/>
<add key="dir:Show contents via cmd" value="cmd:dir #PATH#"/>
<add key="dir:Show contents and open cmd" value="cmd.exe /k dir "#PATH#""/>
<add key="dir:Open directory using shell" value="shell:#PATH#" />
<add key="dir:Open in PowerShell" value="powershell.exe"/>
<add key="dir:Open in pwsh" value="pwsh.exe"/>
</appSettings>
</configuration>
There are two sets of context menu commands: those for the directory list, prefixed by dir: and those for the rule list, prefixed by rule:. The rest of the key is the title of the context menu. The value is a command to run. Here also, there are prefixes:
- powershell: - run the command in classic powershell. Powershell is started with a bunch of fixed options (-NoLogo -ExecutionPolicy Unrestricted etc.)
- pwsh: - same, only for the new PowerShell Core
- cmd: - start cmd with the command
- shell: - use ShelExecute on the folder
- If there's no prefix, the command is run "as-is".
The sample config-file above results in these context menus:
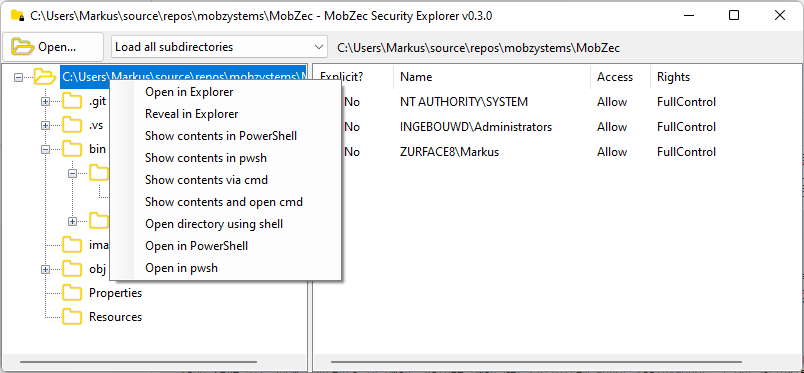
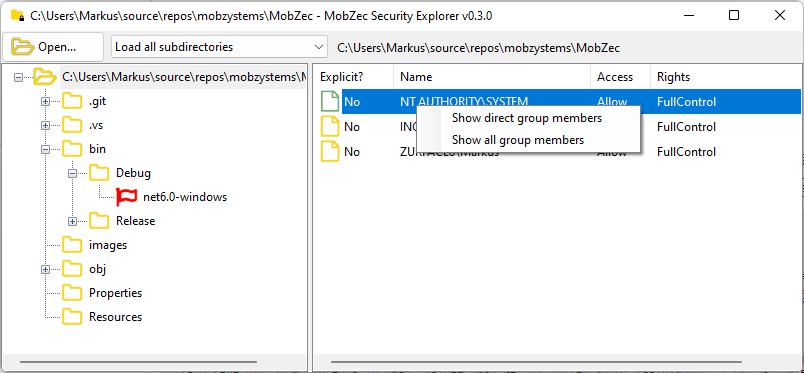
Your mileage may vary: the correct version of PowerShell needs to be installed (Desktop or Core) on your PC, and even Get-AdUser doesn't work unless support for it is installed. But at least you can experiment and add your own menus. It there's no config file present, the standard directory menu will show "Reveal in Explorer" (which wil be removed when custom directory menus are found) and there will be no rule menu.
Async everywhere
Since this is a .NET 6 project, I tried to do things "right". The loading of the directory structure can take a while and you want to be able to cancel while it's loading. Using a Task this turned out to be quite simple. Also, a status bar at the top displays the subdirectory that's currently being loaded, but updating that can slow down the whole process, too. So this status is only updated a few times per second. Lastly, the first level of the tree view is updates during loading which also gives some feedback on progress.
All in all, this tool is remarkably like MOBZHunt - and I'm seriously contemplating rewriting that in .NET 6. I expect to write less code and have a faster, better looking, 64-bit version! Update: done, see MOBZize.
Version 0.3.2 adds a proper installer, enabling the context menu "Open in MOBZec Security Explorer", and even checks for updates!
Download MOBZec Security Explorer
Happy with this tool? Consider buying us a cup of coffee